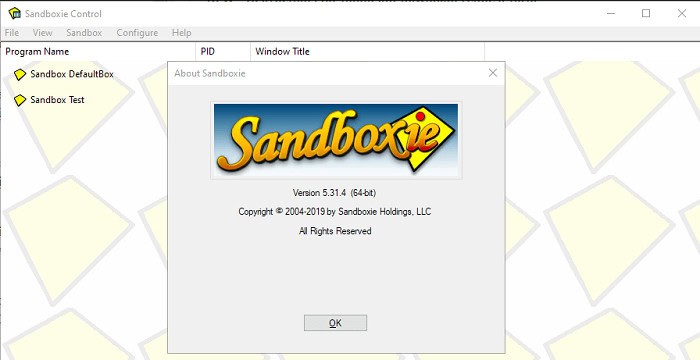
Sandboxie is a program for isolating applications or creating a virtual operating environment for controlled testing of untrusted programs and web surfing. It is a means of protecting your data ultimately. It is widely used to tighten the security against viruses, malware sites, rootkits, etc. Sandboxie can be upgraded to its many settings to enhance the security system for an almost cent-percent guarantee.
A few Sandboxie alternatives are SHADE Sandbox, Firejail, Shelter, Shadow Defender, Cuckoo Sandbox, Windows Sandbox, Island, and Any Run.
Due to various reasons, if you are looking for Snadboxie alternatives, this article is for you. We have listed the best Sandboxie alternatives to try in 2024.
 See Also: 5 Best Audible Alternatives To Try In 2024
See Also: 5 Best Audible Alternatives To Try In 2024
9 Best Sandboxie Alternatives
There is a wide range of Sandboxie alternatives available for our rescue. Let us see the best 9 Sandboxie alternatives here.
Shade Sandbox
Shade Sandbox is developed by Eugene Balabanov and written in C++ language. API spy and virtual environments. 5/5 stars by Findmysoft. Powerful safety filter for running selected applications. It also isolates history, cookies, and temporary internet files. Keeps a check on internet downloads by running them in an isolated environment. Protection for system files, registry entries, and other data. Safe surfing of web pages and email access. 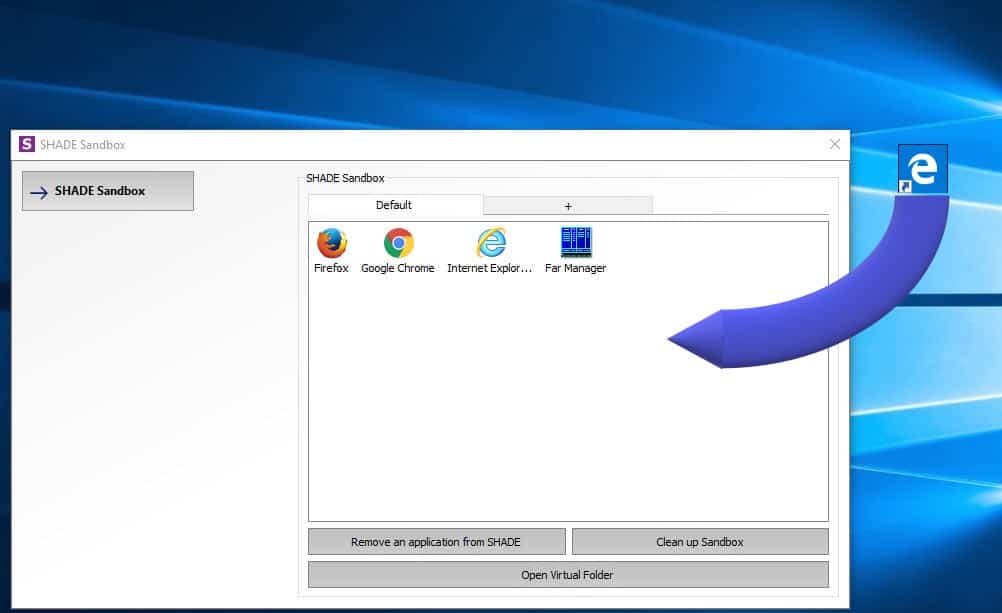
The feature that stands out is its drag and drop of applications makes it sandboxed. No extra configuration or permission is required. In my opinion, it is one of the best result-oriented applications out there. Hence stands first in the list of Sandboxie alternatives.
See also: How to Fix Bluetooth Not Available on MAC Error
Firejail
The next one on the list of Sandboxie alternatives is Firejail. The program is in C language. It is lightweight, has low overhead, has no complicated configuration, and has no open socket connections. 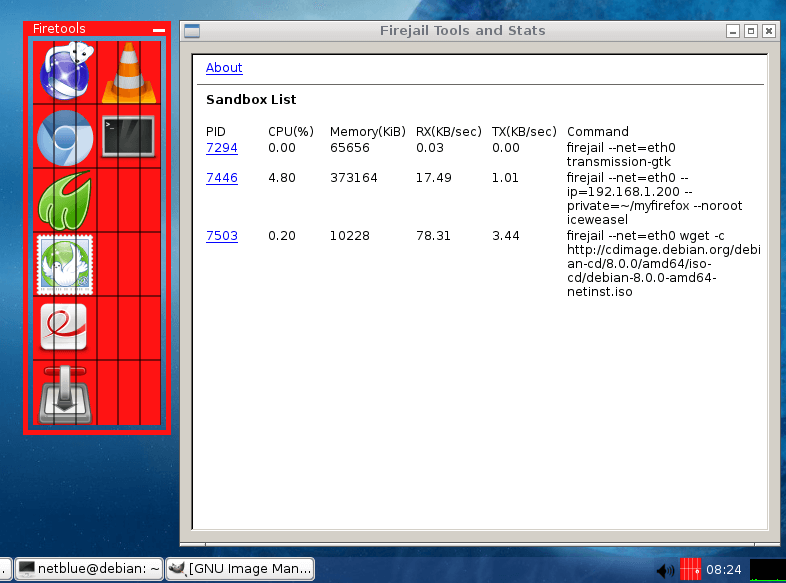 It decreases the risk of security breaches by restricting running environments of untrusted applications using Linux namespaces and seccomp-bpf.
It decreases the risk of security breaches by restricting running environments of untrusted applications using Linux namespaces and seccomp-bpf.
Cameyo
The browser can work within any digital workspace without using any VPN. It also allows work from home without a VPN. You don’t require a particular infrastructure. Fast to deploy. 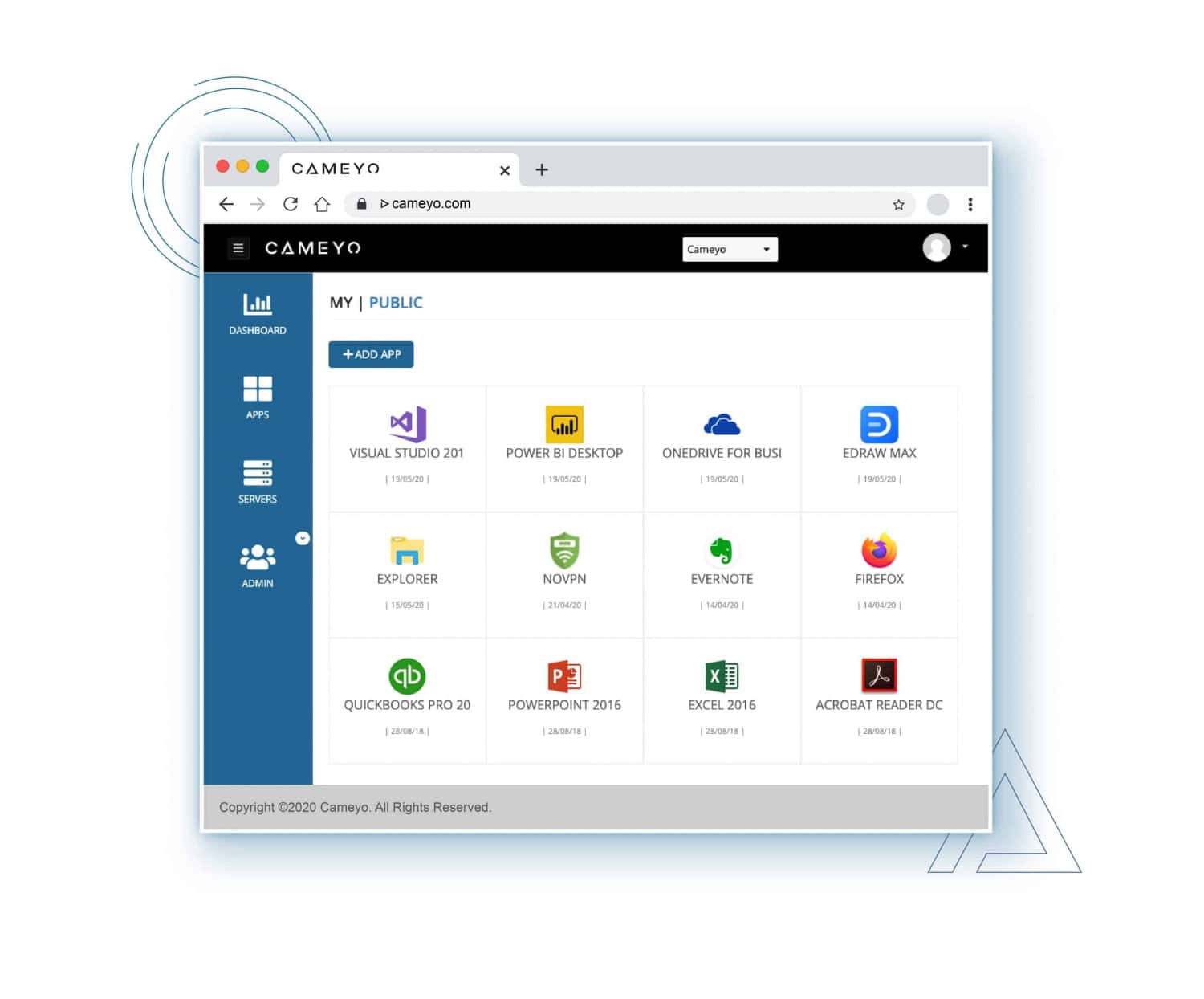 It’s designed for cloud service that runs in any environment- cloud, hybrid, or on-premise. Built-in security features include HTTPS, single sign-on, and separation of apps from operating systems.
It’s designed for cloud service that runs in any environment- cloud, hybrid, or on-premise. Built-in security features include HTTPS, single sign-on, and separation of apps from operating systems.
See Also: How To Get Kinemaster For PC Without Bluestacks?
Shadow Defender
This is one of the Sandboxie alternatives that nullifies system downtime and maintenance. In addition, it can run in a virtual environment called “shadow mode,” which redirects system changes to a virtual environment with no change to your natural environment. 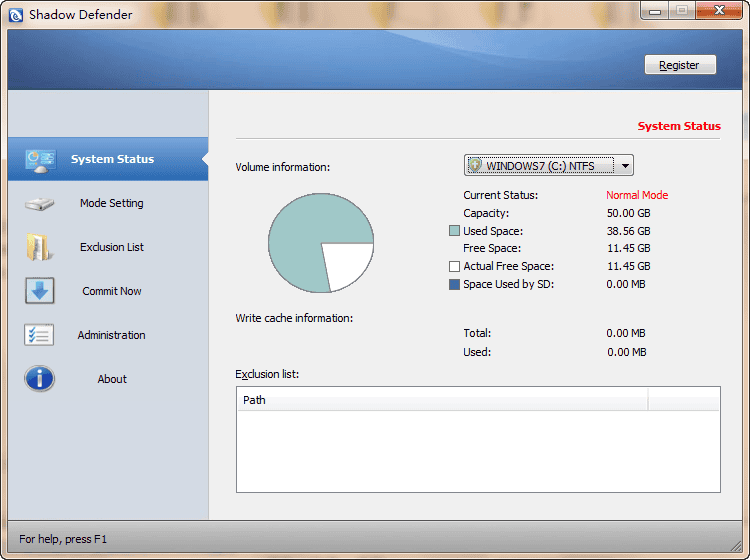 It maintains malicious activity-free software and tests software and game installations in a safe and secure environment. It aids with one of the best flexibility features to permanently select files and folders to the natural environment, guaranteeing they are safe even after reboot. Suitable for workplaces and educational institutions as it protects from unwanted changes by shared users.
It maintains malicious activity-free software and tests software and game installations in a safe and secure environment. It aids with one of the best flexibility features to permanently select files and folders to the natural environment, guaranteeing they are safe even after reboot. Suitable for workplaces and educational institutions as it protects from unwanted changes by shared users.
Cuckoo Sandbox
It is a leading open-source automated malware analysis system. The extensive modular design helps in customizing any aspect of the analysis environment. It renders easy Integration into the existing framework. It uses YARA for processing memory granularity. 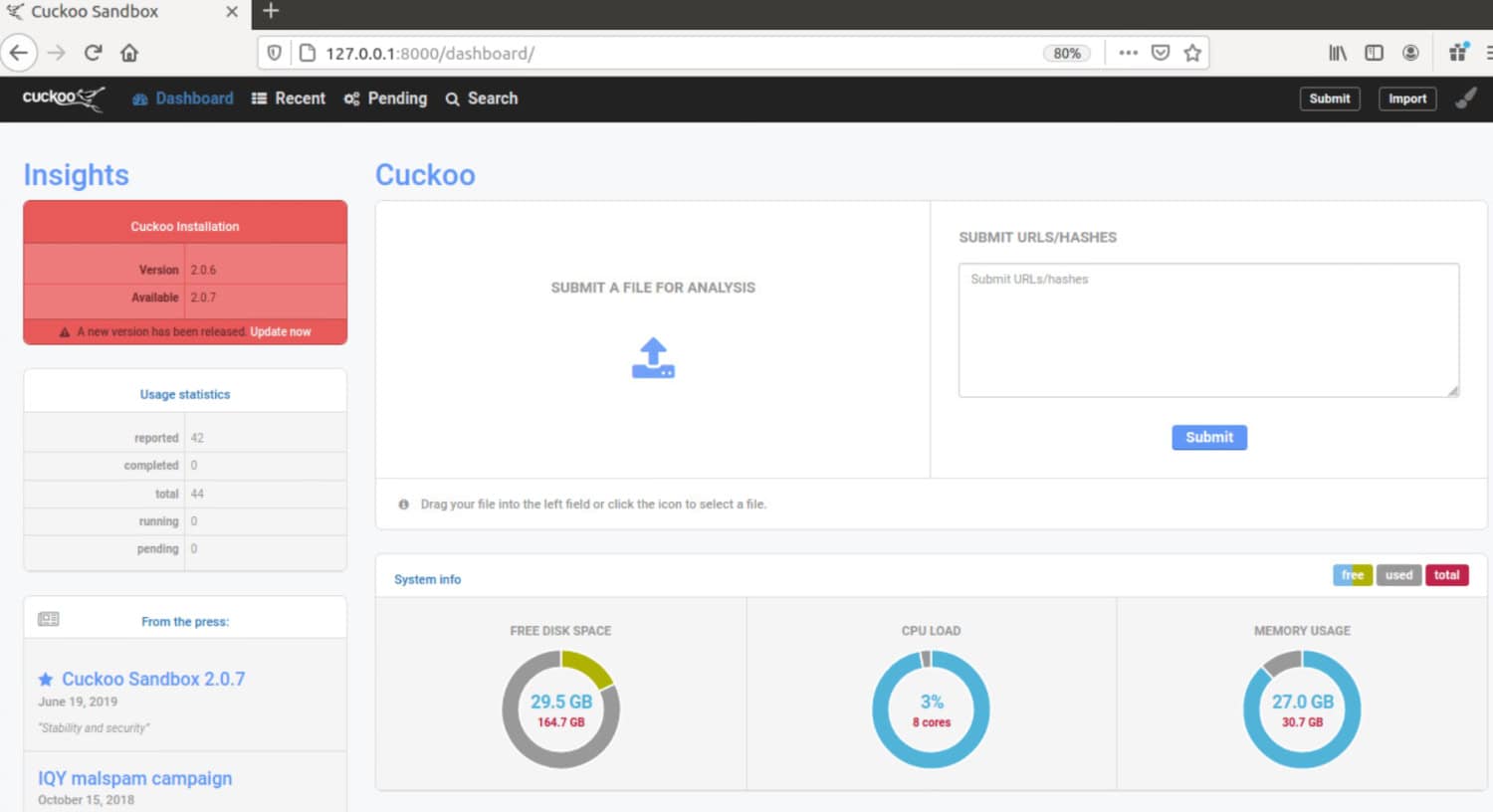 Kernel level behavior monitor, multi-platform analysis. Infinite application opportunities are available on this platform. An elite group of selected hackers, who constantly update their platforms, run these applications.
Kernel level behavior monitor, multi-platform analysis. Infinite application opportunities are available on this platform. An elite group of selected hackers, who constantly update their platforms, run these applications.
Buffer zone
It isolates the application environment completely. Thus, the container’s boundaries will prevent an attack and never allow it to reach the target. It possesses a virtual container, secure bridge, and endpoint intelligence. 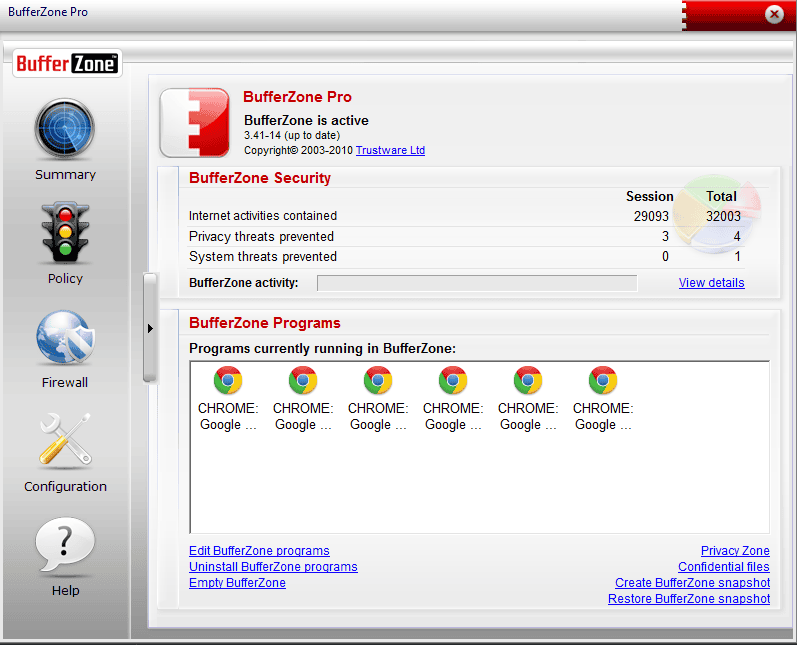 It protects against advanced malware, APTs,zero-days, drive-by downloads, phishing attacks, simple management, quick deployment, and ready set up, and even covers removable storage. Additionally, it helps businesses of all sizes with proxy-based enforcement.
It protects against advanced malware, APTs,zero-days, drive-by downloads, phishing attacks, simple management, quick deployment, and ready set up, and even covers removable storage. Additionally, it helps businesses of all sizes with proxy-based enforcement.
Mbox
Mbox is the next one on the list of Sandboxie alternatives. It is also known as the Berkeley format. It is a standard format for storing email on a hard drive and holds a single, long test file mailbox for each message. The database files do not have a magic number. 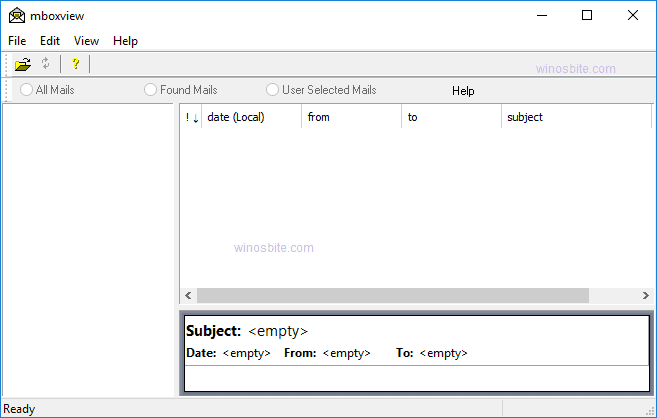 Still, you can identify them by the leading character sequence of “From,” followed by a single space character and additional printable data. Daniel J Bernstein developed this naming scheme, Rahul Dhesi and others in 1996.
Still, you can identify them by the leading character sequence of “From,” followed by a single space character and additional printable data. Daniel J Bernstein developed this naming scheme, Rahul Dhesi and others in 1996.
Comodo Internet Security (CIS)
It is the top-rated product by AV-TEST. It poses advanced host intrusion prevention. Valkyrie system tests their behavior in real-time. It is a great memory firewall against buffer overflow attacks. In addition, it has all the features like anti-malware,anti-rootkit, anti-spyware, anti-virus, and bot protection.  It deploys multi-layered security against hackers. First and most importantly, it automatically sandboxes unknown files and tracks then destroys any existing malware hiding in your computer. It is executed under CIS 6.3, which gives fewer pop-ups, ease of use, and better security.
It deploys multi-layered security against hackers. First and most importantly, it automatically sandboxes unknown files and tracks then destroys any existing malware hiding in your computer. It is executed under CIS 6.3, which gives fewer pop-ups, ease of use, and better security.
Any Run
It is 1st malware interactive analysis sandbox. Here users can control the analysis flow. Cloud-based interactive access tracks behavior activities in real-time. 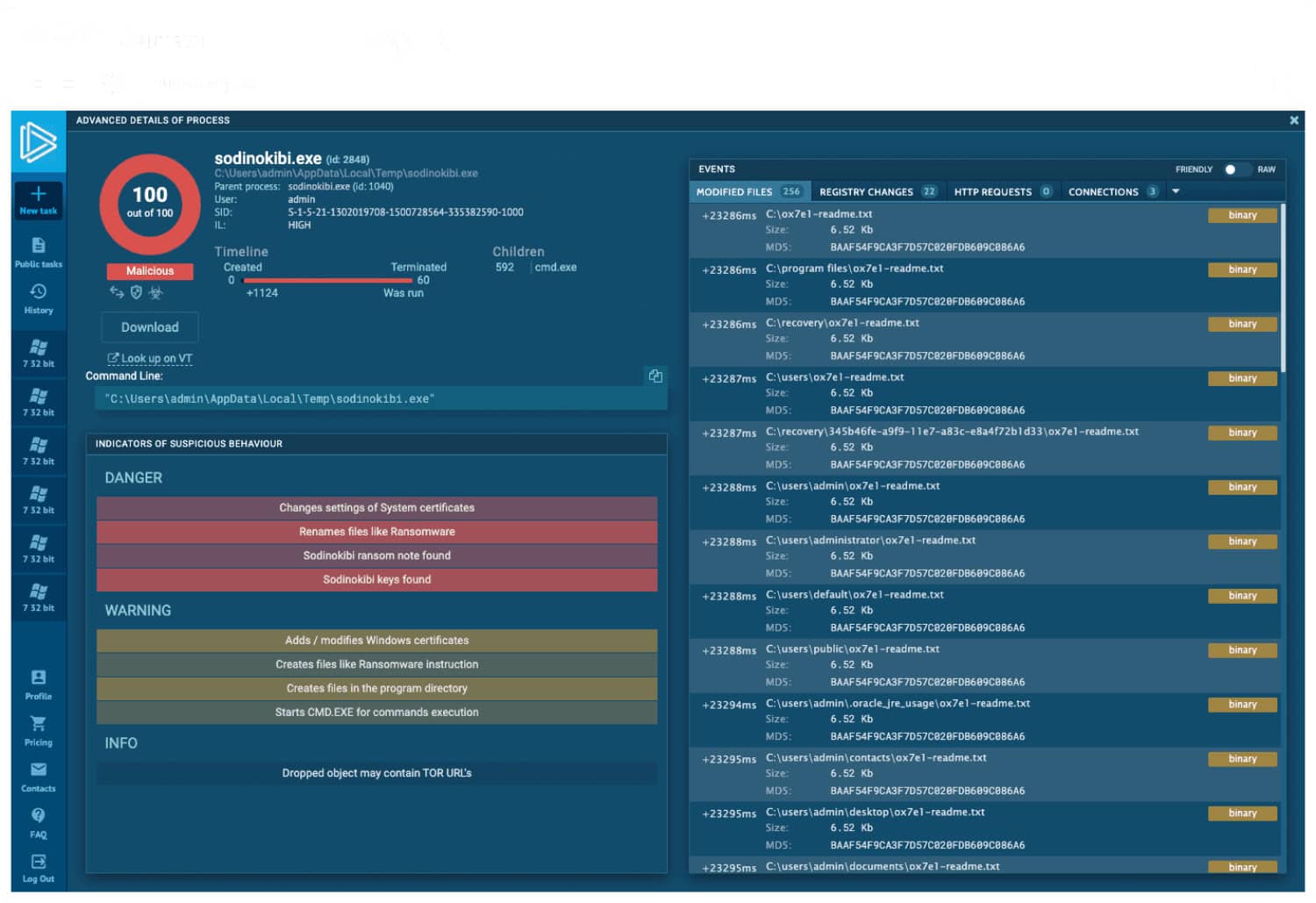 A community of a more significant number of researchers across the globe gives inputs to the threat intelligence platform. This results in analyzing attacks at their appearance, revealing IOC at the initial stages.
A community of a more significant number of researchers across the globe gives inputs to the threat intelligence platform. This results in analyzing attacks at their appearance, revealing IOC at the initial stages.
See Also: Top 7 iOS Emulator for PC | Run iPhone Apps on Windows
Other Sandboxie Alternatives
Apart from these 9, here are some other competitive Sandboxie alternatives for your convenience.
- ReHips.
- VPN Pro.
- Paypal.
- Psiphon.
- Win Jail.
- Forticlient.
- Evalaze.
- Window Sandbox.
- Spoon.
- Microsoft application virtualization.
- VMware Thin App.
- Enigma virtual box.
- Deep freeze.
- Docker hub.
- Apache Mesos.
- Open VZ.
- runc.
- StorageOS.
- CoreOS.
- Oracle cloud infrastructure compute.
FAQS
Why do I need a Sandboxie alternative?
You may need a Sandboxie alternative if you're looking for similar software that offers more features, better performance, or is more affordable.
How does Comodo Internet Security compare to Sandboxie?
Comodo Internet Security is a feature-rich security suite with a sandboxing feature, making it a good alternative to Sandboxie. It offers more features like antivirus protection, firewall, and intrusion detection.
What is BitBox?
BitBox is open-source sandboxing software that isolates applications from your computer's operating system, preventing them from permanently changing your system.
How does BitBox compare to Sandboxie?
BitBox is a lightweight and easy-to-use sandboxing software that offers good security features. It's free and open-source, making it an excellent alternative to Sandboxie for users on a budget.
How does Shade Sandbox compare to Sandboxie?
Shade Sandbox offers more advanced security features than Sandboxie, which additionally makes it a good alternative for users who need more robust security. However, Sandboxie may need to be more user-friendly.
What is Cuckoo Sandbox?
Cuckoo Sandbox is open-source sandboxing software that analyzes the behavior of potentially harmful files and software in a virtual environment, providing detailed reports on their activities.
Conclusion
Before you install any Sandboxie replacement, make sure you check the requirements and suitability. This is important, especially if you’re paying for it to maximize your investment.
We hope this information helps you make a better and more informed choice to increase your security without any significant changes in the local system. Unfortunately, due to rising cybercrimes and the threat, taking precautions to safeguard delicate data and fundamental privacy is the need of the hour. Stay one step ahead of cyber threats! Browse Safely!
See Also: How To Make DeSmuME Faster | 4 Effective Methods

Sourabh Kulesh, Chief Sub Editor at Gadgets 360. and TechiePlus, writes technology news online with expertise on cybersecurity and consumer technology.

